The timing was perfect on this one.
Last week, just as I finished writing a story about “unauthorized activity” on Chipotle's payment system, I received an email alert from Starbucks. It contained a receipt for reloading $100 onto my Starbucks mobile app, using my saved credit card.
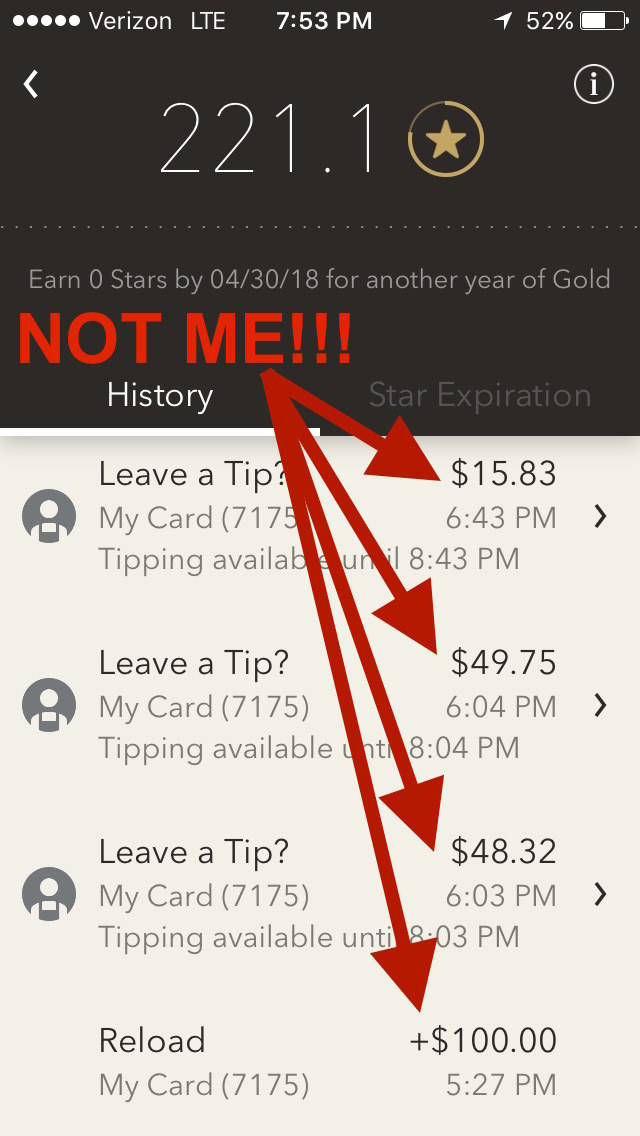
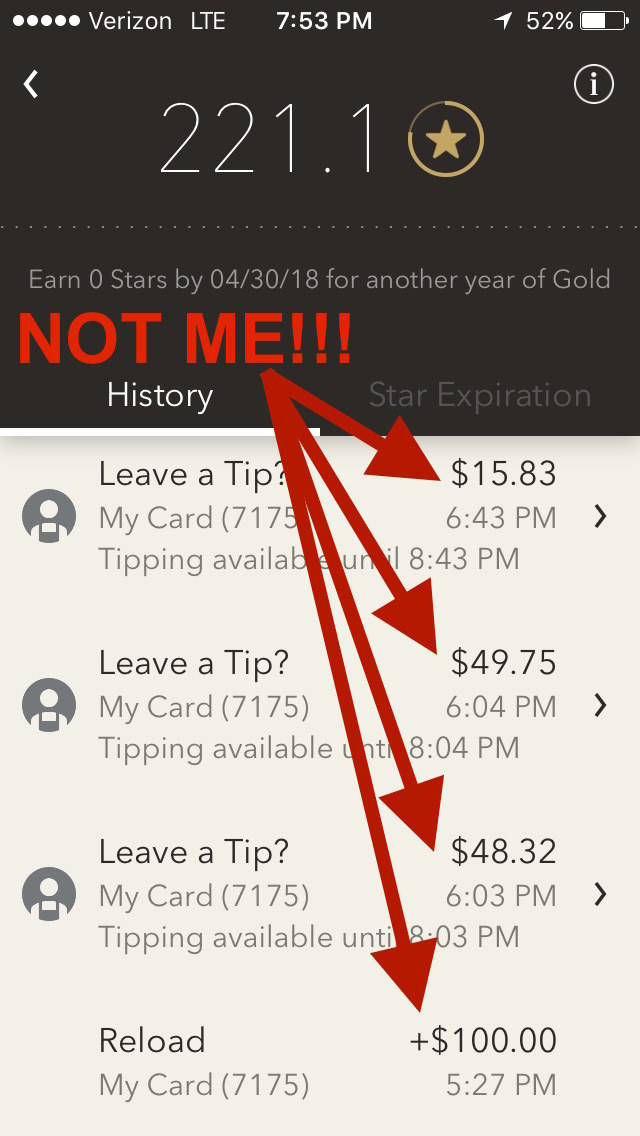
The problem, of course, was I had nothing to do with that transaction. By the time I opened the app to see what was going on, the fraudster had already made three purchases at a Starbucks in San Diego: one for $48.32, one for $49.75, and another for $15.83.
By the time I was on the phone with customer service, my account had been completely emptied.
This is not a new thing — it's called an account takeover, and it's a long-running problem in the Starbucks app. In 2015, customers of the coffee chain reported having their accounts reloaded using their stored credit cards and then emptied, possibly onto gift cards that the scammers then sold at a discount on the black market.
At the time, the company said because many consumers reuse usernames and passwords on multiple sites and apps, criminals were obtaining stolen logins from hacked websites, and trying them out in the Starbucks app.
“We have a team of engineers dedicated to advancing our security and fraud prevention capabilities,” the company said in a statement at the time.
But two years later, the Starbucks app still seems vulnerable to exactly the same weakness. Despite the app being linked to people's credit cards, and capable of charging money to them at will, the company confirmed to BuzzFeed News that it does not support two-factor authentication — a widespread security measure that typically involves the user being sent a code via text message or email when attempting to log in from a new device.
It's a notable weakness, given that mobile payment now represents about 25% of all Starbucks transactions. For a chain that brought in $13.2 billion in sales in fiscal 2016 just through company-operated stores in the US, Canada, and Latin America, that means billions of dollars flowing through the app.
“Relying on usernames and passwords is a failure because no matter what you do, there will always be some percentage of users, probably double digits, who will use a password that they used somewhere else,” said journalist Brian Krebs, author of KrebsOnSecurity.
“I was surprised that in two years, Starbucks hasn’t gotten more aggressive,” said Rob LaMear, CEO of US Cyber Vault. LaMear said his and his wife's Starbucks accounts were both recently compromised. With a global brand, there's “a lot of volume at play here.”
A Starbucks spokesperson said in an email to BuzzFeed News “while account takeover (ATO) activity is an industry wide challenge, we see only a tiny fraction of one percent of our account holders impacted.”
Meanwhile, a slow trickle of complaints from Starbucks customers continues to emerge on social media.
Like many other big restaurant chains launching their own ordering and payment apps, mobile is a critical part of Starbucks' growth plan. While repeat customers are big fans of the convenience of these apps, the companies also benefit from the reams of highly-detailed data they collect on customer habits.
How serious is Starbucks about getting digital right? It's newly-appointed CEO, Kevin Johnson, was previously the CEO of tech company Juniper Networks, and was a senior executive at Microsoft before that. Last month, Johnson singled out “digital relationships with customers” as one of the company's “most important things for the future.”
Asked about rolling out two-factor authentication, Starbucks said, “While we do not share specifics on future security protocol timelines or practices, our security and anti-fraud teams actively continue to develop, and invest in, enhanced protection measures, further strengthening our platforms.”
Starbucks customer service said they would cancel the $100 charge with my credit card company and refund the balance that was on my account before it was compromised. The representative had me change my password while I was still on the phone with her.
Was your Starbucks account compromised? To contact the reporter on this story, email venessa.wong@buzzfeed.com, or go to tips.buzzfeed.com to learn how send your tip securely.
Quelle: <a href="People Broke Into My Starbucks App And Charged Me 0“>BuzzFeed